Combating Cybercrime: Significant Success Against the Platform Phishing W3LL
A triumphant victory in the battle against cyber-piracy was recently achieved with the coordinated operation of FBI Atlanta Field Office and Indonesian authorities, who brought an end to a phishing operation that had deployed the “W3LL” platform globally. The disruption of this platform was not just a local operation, but a pivotal point of cooperation between the United States and Indonesia to combat an alleged cybercriminal. The operation led to the seizure of infrastructure and the arrest of the developer, highlighting the importance of international cooperation on cybersecurity.
The W3LL Store Threat
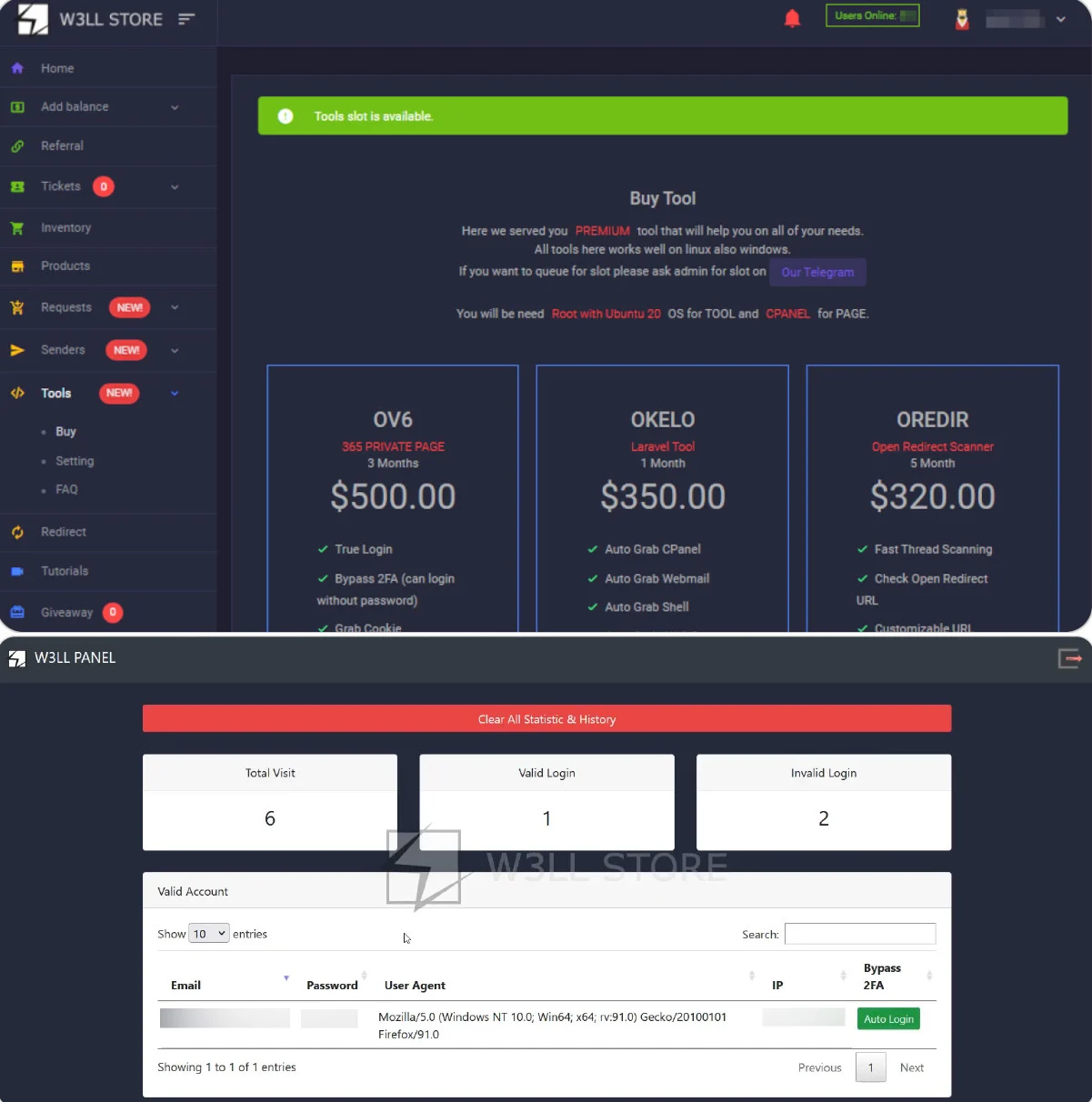
The W3LL platform was not just a simple phishing kit. It had evolved into a fully functioning marketplace that made it easy for cybercriminals to steal employee credentials and attempt to make huge sums of money, estimated at over $20 million in attempted fraud. The W3LL Store operated as an online marketplace where phishing kits were sold and larger scams were accomplished through the collection of personal information and organized attacks.
“This website was seized as part of a coordinated law enforcement action,” reads a related seizure message displayed on the W3LL website.
How the Phishing Kit Works
W3LL Store offered a phishing kit for sale for $500, ensuring that attackers could replicate convincing copies of corporate login portals. This tool allowed criminals to capture detailed login information, bypassing multi-factor authentication (MFA) and gaining access to compromised accounts, posing a critical threat to the security of our digital presence.
Source: Group-IB
Market Development and Business Attacks
The W3LLSTORE marketplace facilitated the sale of more than 25.000 compromised accounts between 2019 and 2023, while, after its closure, its operations continued through encrypted communication platforms, with entities repurposing and selling their toolkit to other criminals.
Consequences and Contemporary Attacks
Between 2023 and 2024, the phishing kit was used to target over 17.000 victims worldwide, with evidence that the developer harvested and resold access to compromised accounts. W3LL had been recognized for its campaigns against modern business accounts, particularly its users. Microsoft 365, planning complex attacks.
The platform relied on “man-in-the-middle” attacks, where legitimate login portals were mediated by attacker infrastructure, allowing for real-time tracking of credentials and session cookies.
Only after gaining access to victims do attackers intercept incoming messages and create rules to commit email fraud and redirect payments.